Cyber Resilience Act
Automated.
Get ready for compliance with the draft standards prEN 40000. Z-CMS automates your CRA gap assessment, policy generation, risk assessment, threat modelling and much more.

What is the Cyber Resilience Act?
The EU's comprehensive cybersecurity regulation for products with digital elements. Requires security-by-design and lifecycle maintenance.
Key Requirements
Reporting Obligations
Report actively exploited vulnerabilities and severe incidents affecting products within 24 hours
Read detailed guideRisk Assessment
Conduct cybersecurity risk assessments to identify applicable CRA essential requirements
Product Requirements
Apply standards to demonstrate that products have sufficient security measures to meet CRA essential requirements
Vulnerability Handling
Put in place processes to handle vulnerabilities in products when they are discovered or reported
Technical Documentation
Create and maintain comprehensive compliance documentation
Test Report
Conduct assessments and document your test results and evidence
Non-Compliance Penalties
Financial Penalties
Up to €15M or 2.5% of global annual revenue
Market Access
Products blocked from EU market, potential recalls
Reputation Damage
Loss of customer trust and competitive position
⚠️ Don't slip up on compliance! The stakes are high, and the deadlines are approaching fast.

What Z-CMS offers today
Comprehensive CRA gap analysis powered by intelligent Q&A based on official draft standards

CRA Gap Analysis
Identify exactly where you fall short of CRA requirements with a guided Q&A based on official draft standards and get a comprehensive report.
Based on prEN 40000-1-3
Vulnerability handling requirements
Based on prEN 40000-1-4
Product security requirements
CRA Annex II Coverage
Information and Instructions to the User
Gap Analysis Dashboard
Dashboard and exportable PDF reports
Task Management Dashboard
Prioritization and real-time compliance tracking
CRA Policy Generation
CRA requires vulnerability handling policies. Generate fully compliant CRA policies in minutes. Stop writing them from scratch — Z-CMS creates them for you, tailored to your organisation.
prEN 40000-1-3 Compliant
Vulnerability handling policy fully aligned with the official draft standard
Saves Hundreds of Hours
Generate complete policies from expert-built templates in minutes
Fully Customisable
Tailor any policy to your organisation — not just templates, but fully bespoke generation
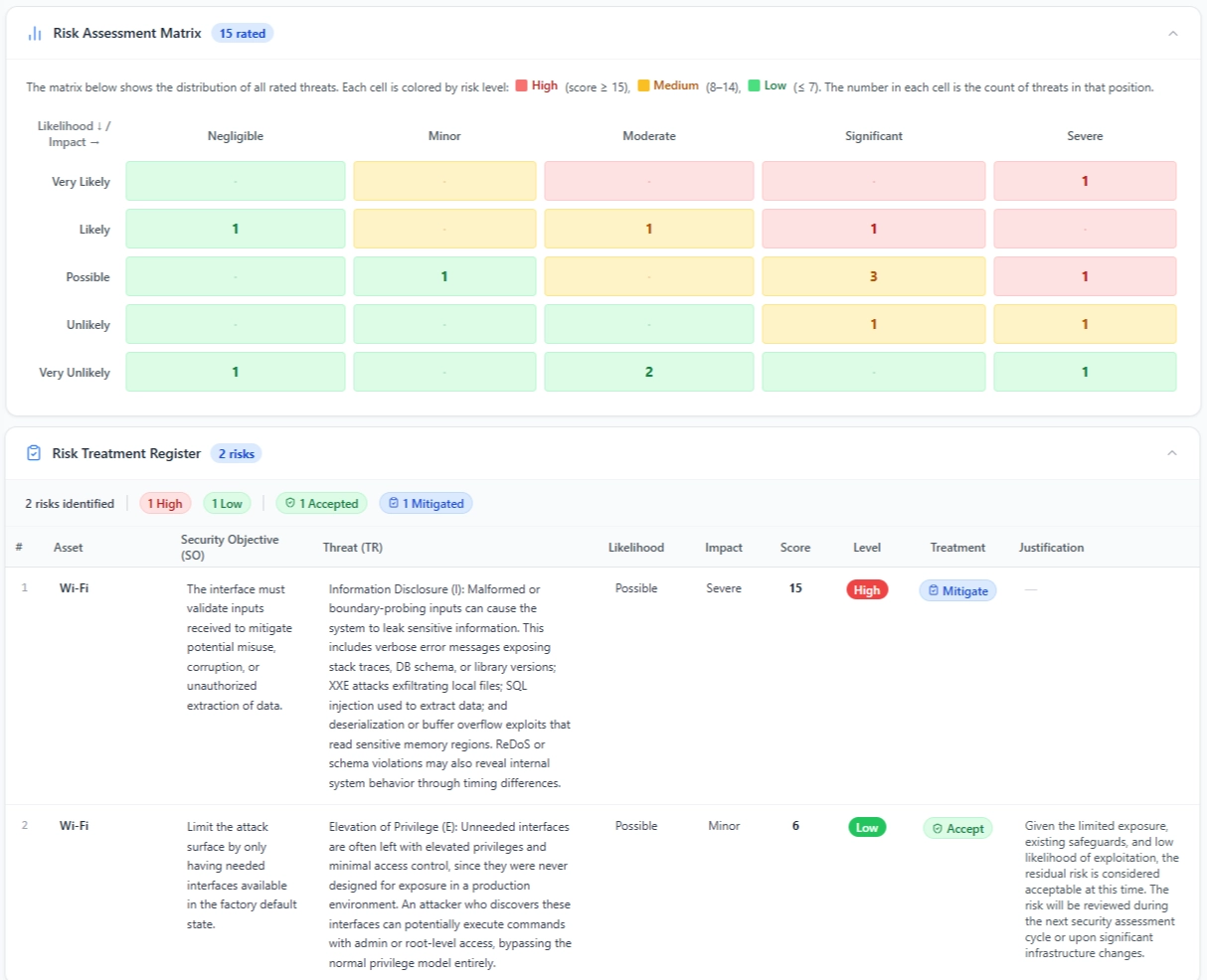
CRA Risk Assessment
Answer our guided Q&A to fully assess your product's CRA risk profile — from classification to applicable requirements — in a fraction of the time.
🎉 Free on zealience.com - Also will be available inside Z-CMS
prEN 40000-1-2 Compliant
Methodology fully aligned with the CRA risk assessment standard
Product Classification
Determine if your product is Critical, Important, or Default class under the CRA
Suitable Standards
Identify which standards apply to your specific product type and context
Threats & Security Objectives
Map relevant threats and define security objectives for your product
Applicable Requirements
Pinpoint the exact CRA essential requirements and prEN 40000-1-4 requirements that apply
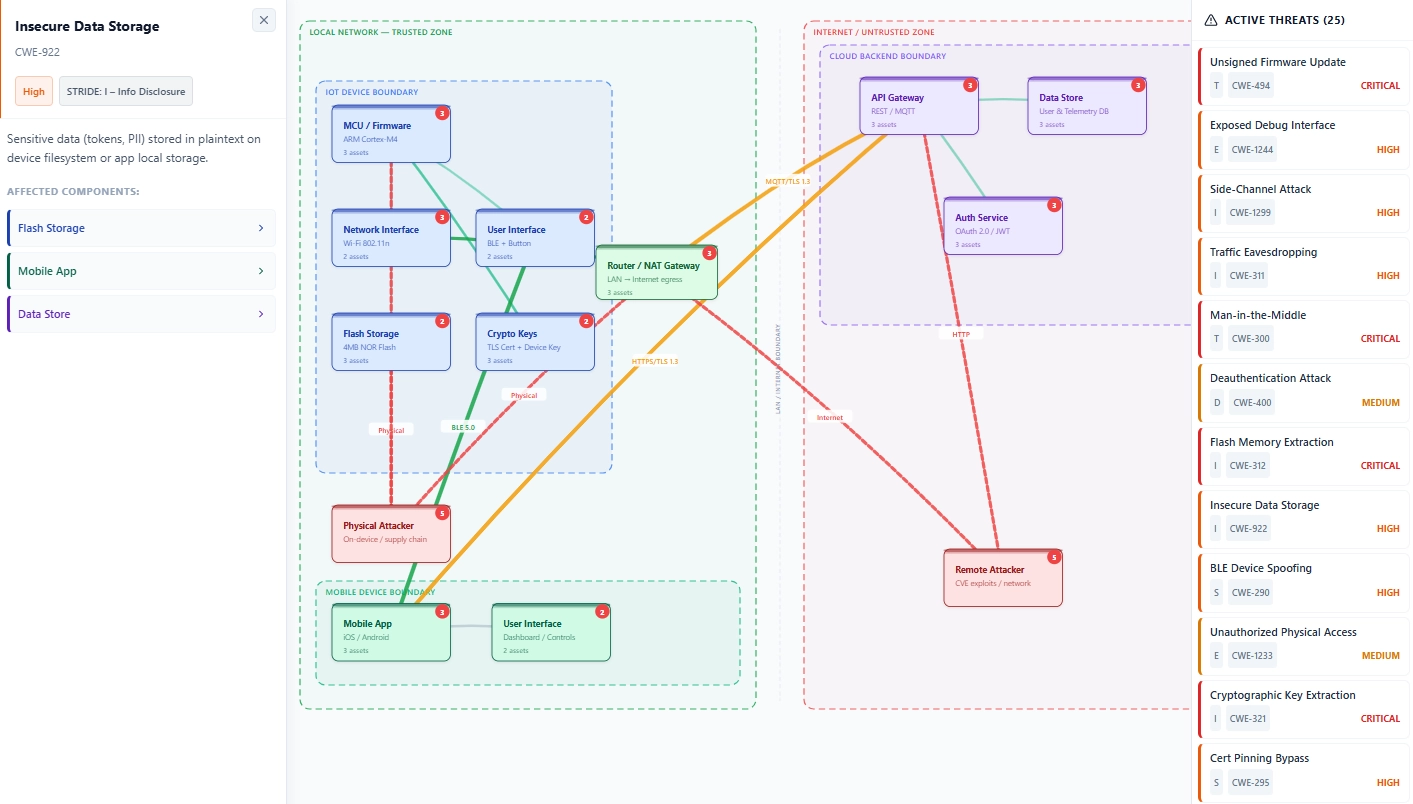
CRA Threat Modelling
Build a comprehensive threat model grounded in your risk assessment, fully aligned with CRA prEN 40000-1-2. Streamline the path from risk assessment to threat modelling in one place.
Architectural Diagrams
Visually model your product architecture with an intuitive diagram builder
Components & Assets
Capture all product components and assets that need to be protected from our catalogue
Threats & Trust Boundaries
Identify threats and define trust boundaries between components
prEN 40000-1-2 Compliant
Threat modelling methodology fully aligned with the official CRA standard
Based on official draft standards: Our features use prEN 40000-1-2, prEN 40000-1-3, prEN 40000-1-4, and CRA Annex II. We'll update as standards are finalized to ensure you're always working with the latest requirements.
Why Z-CMS?
Built by IoT cybersecurity compliance experts, trusted by manufacturers worldwide

Proven Track Record
Zealience has supported hundreds of manufacturers worldwide with RED DA / EN 18031 compliance. With two-thirds of EN 18031 expected to be reused in prEN 40000-1-4, Z-CMS stays relevant as regulations evolve.
See success stories
Expert Leadership
Our R&D is led by Dr. Guillaume Dupont, with over 10 years of experience in IoT cybersecurity and compliance. In a field where interpretation errors lead to costly non-compliance, expert guidance is critical.
Meet the team
On-Premises Security
Your data never leaves your environment. Z-CMS runs on-premises inside your network and firewalls. Zealience has no access to your data—no SaaS analytics, no AI training, no external processing.

Industry Network
With deep industry experience, Zealience connects you to trusted consultants, legal experts, and Notified Bodies—delivering end-to-end compliance support in a field where expertise is scarce.
View servicesZ-CMS CRA Roadmap
Building a complete CRA compliance solution as standards are finalized
CRA Gap Analysis
Automated gap analysis with comprehensive report
CRA Policies Generator
Automated generation of CRA-compliant policies and procedures
Risk Assessment Tool
Comprehensive cybersecurity risk assessment tailored to the CRA
Vulnerability Manager
Track, document, and manage product vulnerabilities
Technical Documentation Generator
Generate complete technical documentation packages
Complete CRA Compliance Suite
Full end-to-end CRA compliance solution
Ready to start your
CRA compliance journey?
Get ahead of the December 2027 deadline. Book a personalized demo or explore our pricing to see how Z-CMS can streamline your compliance process.
Trusted by manufacturers worldwide
